Control the Risks of IoT and BYOD in Healthcare: Part II
April 4, 2019

Lightedge
Author

This is the second in a two-part series on issues related to the IoT, BYOD and cybercriminal attacks on ePHI. We suggest starting with part I if you have not read it.
The internet of things (IoT) includes personal mobile devices and wearables that employees and contractors use daily, inside and outside of the workplace. Drawing boundaries for device regulation has been a challenge for leadership teams, as the line between professional and personal are blurred. It is clear, however, that healthcare organizations who take a proactive approach to secure all network-connected devices and ePHI gain an advantage. They reduce the risks for HIPAA violations, costly data breaches, and reputational damage.
“The challenge is that mobile technology and all of its related benefits have become the norm in real-time communication in our society. When applied to the healthcare space, however, a person’s privacy and security must be considered equally as important as convenience and cost,” said Guillermo Moreno, vice president and managing director at Experis Healthcare Practice.
Why Do Health Care Organizations Gravitate Toward BYOD?
Advancements like BYOD (Bring Your Own Device) capabilities appeal to companies because they reduce immediate costs, enhance collaboration, and give employees access to current technology. BYOD eliminates the need for professionals to carry around two phones and often encourages creative problem-solving.
In the healthcare industry, BYOD can offer professionals increased flexibility, fast access to pertinent information, and it can be used to enhance patient services. The BYOD market is on target to reach nearly $367 billion by 2022, up from just $30 billion in 2014, reports Insight. Yet, without BYOD policies, some organizations simply cannot fund these new advancements.
BYOD and the Internet of Things (IoT) go hand in hand. Some employers will look to create internal company apps and project management systems, while others will mandate that certain security programs and external apps and management systems be installed on devices to maintain compliance.
BYOD Vulnerabilities and Cyber-Attacks
BYOD programs create multiple vulnerabilities within an organization’s technical framework. One device can present several weaknesses including:
- Internet connectivity. Within a private network or on a cellular network, device users enjoy relative safety. If users connect to public Wi-Fi, however, they expose themselves to criminals running software to scan for entry points.
- Social engineering. How a user behaves on a mobile device also affects its cyber-vulnerability. In socially engineered attacks, an employee may unwittingly play a role in a data breach. Using a plea for help, a notice from a bank, or a compelling offer, criminals bury malicious software within seemingly legitimate messages.
- Theft. According to the Office of Civil Rights, one of the top reasons for a healthcare data breach is theft. If a mobile device is lost or stolen, it should be reported immediately. If the device has protected health information stored on it, then a healthcare organization could be faced with a data breach.
These examples represent a limited number of tactics criminals may use to gain access to protected health information. If a criminal intends to compromise ePHI, he or she may try to access both data in motion (during transmissions) and data at rest (while stored). Organizations can invest in a current BYOD policy, technical safeguards, and employee education to minimize the risks associated with these and other vulnerabilities discussed in part I.
Audit Existing BYOD Policies
HIPAA regulations, especially the HIPAA Security Rule, provides cybersecurity guidance but does not constitute a set of comprehensive standards or BYOD rules. In addition to the existing HIPAA regulations and recommendations, healthcare organizations need to consider vulnerabilities associated with the IoT, network security, and physical infrastructure.
Audit existing BYOD policies with a wide cybersecurity lens. Failing to do so ultimately puts ePHI at risk. Keep in mind that BYOD is always evolving, and with that so should your organization’s policies.
Ever since the beginning of smartphones and tablets, workplaces have been adopting and evolving toward BYOD. With Tech Pro Research reporting that 72 percent of workplaces will be adopting BYOD in the year to come, many businesses are preparing in advance of streamlining integration.
In the future, change in policy will also occur. As telecommunications providers increase data usage limits and reduce restrictions, employers will no longer have to “foot the bill on data,” and many won’t be willing to, according to Tech Pro.
To maintain compliance and manage BYOD in the workplace, consider the following components within a BYOD policy that go beyond regulatory compliance:
- Relevancy. Every technology-based policy relies on its current relevancy. Review and update the existing policy as needed to account for changes in the threat landscape, device advancements, and industry best practices.
- Attack prevention and management. Many BYOD policies cover the basics, including system setup and regulation compliance, but fail to address additional cybersecurity considerations. Outline prevention and response activities to clarify in-house processes.
- Rights and responsibilities. Organizations set up BYOD programs differently, but any technology policy represents a two-way street. The organization plays a role in security and data privacy, as does the user. Clearly outline each device owner’s rights and responsibilities, including device/app/data ownership, and how the business may interact with their personal information on a device.
Consider the policy as a subset within a larger cybersecurity program. Incorporate general cybersecurity considerations as they apply to mobile device usage to cover all components.
“Ultimately, the requirements for securing the IoT will be complex, forcing CISOs to use a blend of approaches from mobile and cloud architectures, combined with industrial control, automation and physical security,” said Ganesh Ramamoorthy, a research vice president at Gartner. “However, CISOs will find that even though there may be complexity that is introduced by the scale of the IoT use case, the core principles of data, application, network, systems and hardware security are still applicable.”
Embrace Technical Safeguards
In addition to a formalized policy, create processes and invest in solutions to improve compliance and overall security. Protect data with the following technical safeguards:
- HIPAA-compliant hosting. All digital hosting solutions must adhere to HIPAA regulations and support the needs of mobile users. Consider solutions that go beyond secure hosting to offer multifaceted security solutions, including risk-auditing services, malware protection, secure log management, and encryption for data in motion and data at rest. Because both you and your service providers are liable under HIPAA, you need a reliable provider with compliance expertise.
- Device and data authentication controls. Two-factor authentication controls on devices and within applications create multiple barriers to commonly targeted endpoints.
- Remote lock/wipe. Organizations can reduce the risk of a data breach and minimize the effects of an intrusion with remote lock-and-wipe functionality on BYOD-approved devices. Mobile device management (MDM) solutions provide remote lock/wipe functionality and other safeguards.
- Encryption. In the healthcare industry, data is more valuable than the device. Consider cutting-edge encryption for data in motion and data at rest to protect health information. Use the Cryptographic Module Validation Program (CMVP) from the National Institute of Standards and Technology to maintain robust encryption standards.
- Conduct regular updates. Updating operating systems regularly is an important part of any security strategy. Hackers target vulnerabilities in operating systems, and installing updates helps close those holes and protect data. Develop a policy of notifying providers of important updates and enforce update requirements.
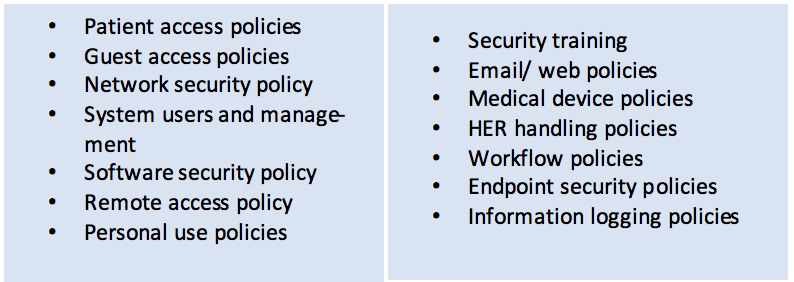
Figure 1: Example Policies for IoT and BYOD
These safeguards protect the devices and the data used in healthcare settings, but one more component will strengthen any BYOD cybersecurity program, employee education.
Educate Employees
Educating employees about new policies, security measures and benefits is critical. While you might know why you are implementing BYOD security regulations, most employees do not know the difference between what is secure and what is not. It is best to start from the ground up when educating team members, so no important details are missed.
Educating staff about BYOD means helping them understand how to interact with the corporate network and how to access proprietary data. If employees are not trained properly, it could lead to unintentional data breaches, malware attacks, or targeted attacks from hackers.
It is important to make education a regular event. Some examples of how to incorporate education into the everyday activities of business include having small meetups to discuss security practices, hosting lunch and learns to incorporate a social aspect to a particularly dry subject matter, or ensure that managers touch base with their employees in individual meetings. When security is not the main focus of someone’s job, it can be easy to forget such things. Scheduling regular reminders can help keep security top of mind for everyone.
According to Ponemon Institute research, factors contributing to data breaches include employee negligence, often associated with their mobile devices and wearables. Educate, train, and remind employees of best practices and the risks of noncompliance. Every person who can potentially access sensitive health information plays a role in safeguarding your assets. Encourage all employees to report suspicious activities and use your organization’s best practices.
Embrace BYOD with Strong Risk Management
The BYOD and wearables phenomenon will only continue to grow. Healthcare organizations should use proactive measures to protect data with the latest security technology on top of what is already required to maintain HIPAA compliance. Create a culture of security for employees, service providers, and patients. Businesses can gain all the benefits of IoT, including mobile devices, without significantly increasing cybersecurity risks.
Feel free to reach out to our team of experts to see how we can help strengthen your IT infrastructure and security posture.
Get Accurate IoT and BYOD Security Detection Today
Despite all of the security risks BYOD poses to an IT environment, the trend of businesses embracing bring your own device in the workplace continues to grow at a rapid pace. With the proper security safeguards in place, healthcare organizations can avoid risks and embrace rewards of BYOD.
Security and compliance not only protect businesses from excessive regulatory fines, it also protects their critical data from threats and breaches. Fortinet’s high-performance security platform has solutions for the core, the edge, and access. The network operating system is flexible enough for deployments of all sizes and environments, from carriers to small businesses.
Use Lightedge’s and Fortinet’s network security fundamentals to protect, monitor and act against threats. Start today by beginning your free Fortinet Cyber Threat Assessment Program and receive a report on your security and threat prevention, user productivity, and network utilization and performance.
In addition to Fortinet’s network security assessment, Lightedge offers secure data center colocation solutions at our Des Moines, Kansas City, Omaha, Austin, and Raleigh data center facilities. As a top-tier colocation services provider, we provide a high level of availability and reliability through secure, certified data centers and dedicated staff onsite.
Lightedge also offers a free risk assessment from our Chief Security Officer and Chief Compliance Officer as a free resource to all of our clients. Lightedge’s highly-trained compliance and security experts take the guesswork out of keeping your business protected. Compliance and security are top priorities to guarantee that your data is protected. Lightedge is compliant with:
If you are interested in getting enrolled in the Cyber Threat Assessment Program, or touring of any of our 7 world-class data centers, contact us here. We have network security experts standing by to answer your questions or to help you begin Fortinet’s free Cyber Threat Assessment Program.
If you would like to learn more about compliance and security download our free E-book, Patient Privacy and Data Security: Utilizing IT Vendors to Meet HIPAA Compliance and Avoid Risks, or you can download our How to Tech Guide for Encryption for Data Security.
Related Posts:
- Control the Risks of IoT and BYOD in Healthcare: Part I
- Electronic Health Records Security: How to Secure your Patient Portal
- What to Look for in HIPAA Compliant Hosting
- 4 Things Your Company Should Know about Internet of Things (IoT) Security
- Top Takeaways from 2018 Verizon Data Breach Investigation
- Healthcare Data Center Trends you Should Care About
- 6 Ways to Noticeably Heighten Healthcare Data Security
- Weighing the Cost of Data Security: Why It’s Important for Large and Small Businesses


